Managing Roles and Privileges in Oracle Fusion Cloud
September 15, 2023
Examining the intricate management of jobs and privileges in Oracle Cloud’s security framework.
Introduction
In today’s digital landscape, securing sensitive data is paramount, especially for administrators and security experts in industries relying on Oracle Cloud – a cornerstone in finance, healthcare, and beyond. This post examines a critical area of Oracle Cloud’s security framework: the intricate management of jobs and privileges
There are multiple layers concerning Oracle’s Cloud security, but we’ll start by unraveling the essential principles of job and privilege management. Therefore, we will share actionable insights and equip you with strategies to fortify your security protocols. Together, we will strengthen Oracle Cloud’s digital defences and safeguard the integrity of your data.
The What and Why
Defining “Roles” and “Privileges”
In Oracle Cloud, ‘Privileges’ refer to specific rights or permissions granted to users or roles, determining the precise actions they can perform within the system. Meanwhile, ‘Roles’ act as containers for privileges, grouping them together for easy assignment of common permissions to users with similar tasks or responsibilities.
Why Understanding Roles and Privileges Matters
Comprehending roles and privileges is fundamental to Oracle Cloud security. Roles streamline the process of granting and revoking permissions, making it more efficient to manage access for different user groups.
Privileges dictate the specific actions a user or role can perform. This level of granularity ensures that individuals have the exact permissions they need and no more. This is crucial for maintaining the principle of least privilege, a cornerstone of security best practices.
Understanding the Risks of Job Roles
While Oracle Cloud’s default job roles offer a convenient starting point for access management, they come with a caveat. These roles often encompass a wide array of permissions, making it challenging to discern the precise scope of access granted.
This opacity introduces a potential risk, as users may inadvertently wield more power than necessary. It is imperative for organizations to carefully review and tailor seeded job roles to align with their specific requirements. Therefore, ensuring that each user possesses only the permissions essential for their role, reducing the likelihood of unauthorized access and safeguarding sensitive data.
The Tricks of Oracle’s Security Console
When considering anything from Roles to Privileges, it is all controlled using the Oracle Security Console. To perform any of the actions looked at today, you will need the ‘IT Security Manager’ job role to gain access to this console.
Once you have this access, you can find it on your Oracle Cloud homepage under Tools > Security Console.
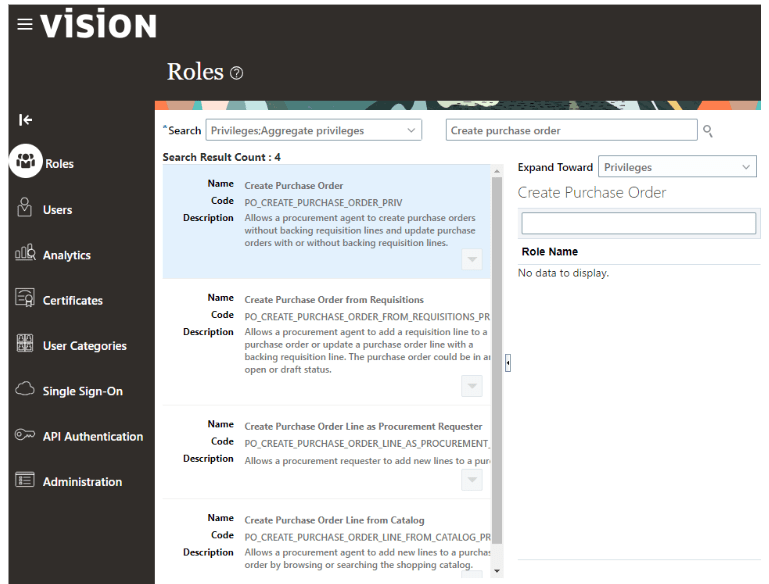
How to Find your Privileges
Oracle Cloud Privileges can be found through the Security Console. From the Oracle Cloud Homepage navigate to Tools > Security Console, then follow the below steps.
- Click on “Roles” on the left hand pane.
- In the “Search” list of values ensure only “Privileges” is checked.
- In the search box to the right, start to type keywords for privileges you are looking for like “Create Purchase Order”.
- The search results will appear and provide a brief description of the privilege.
- These privileges can be used in the “Create your own Custom Roles” section of this blog.
Create your own Custom Roles
By creating your own custom roles you can explicitly list out the privileges you need, then accurately assign it to your users.
Steps to create your own roles are as follows:
- Navigate to the Security Console from the Oracle instance homepage via Tools > Security Console.
- Click “Roles” from the left hand pane.
- Click “Create Role” in the upper right hand corner of the console.
- Fill in the necessary information:
- Name and Code: provide a descriptive name for the custom role like “Purchase Order Creates Only Role”.
- Role Category: select the functional area for the role like Procurement – Job Roles.
- Description: optional, add a brief description.
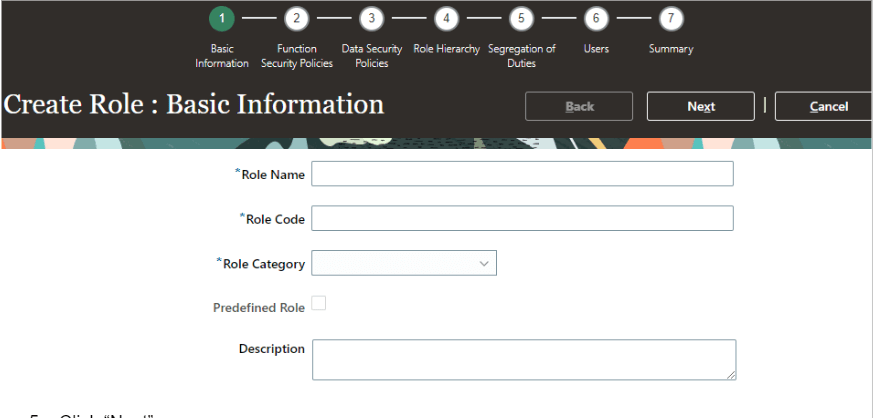
5. Click “Next”.
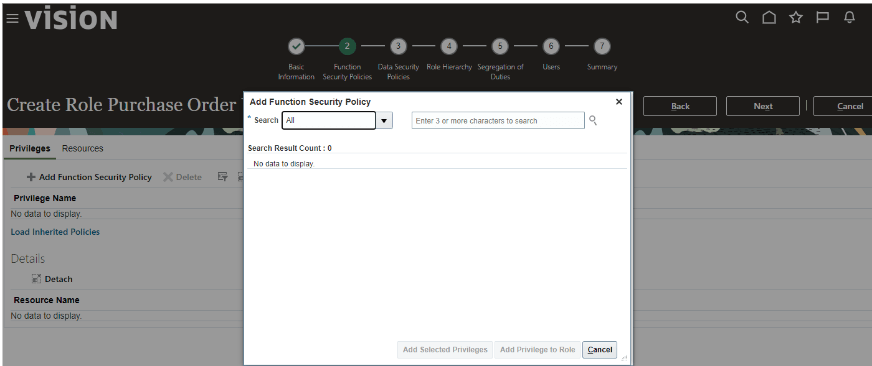
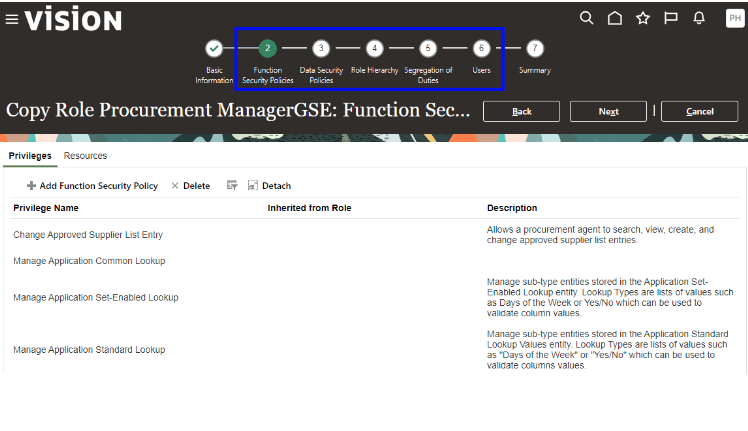
6. Use the “Function Security Policies” area to now assign your privileges to your role. Do this by clicking “Add Function Security Policy” and a window will appear to search and add your privileges.
7. Once all privileges are added, navigate to the users step where you can add the role to your users. This can always be done later via the Security Console.
8. Lastly, navigate to the summary page and click ‘Save and Close’.
Copying Existing Roles
Another trick you can do is copy an existing Oracle Job Role and make it yours. Oracle’s default Job Roles are not updateable, but you can copy them to make life easier.
By copying the existing Job Roles, you can strip out what you don’t need and add the extras that you do need. To make a copy of a role follow the below steps:
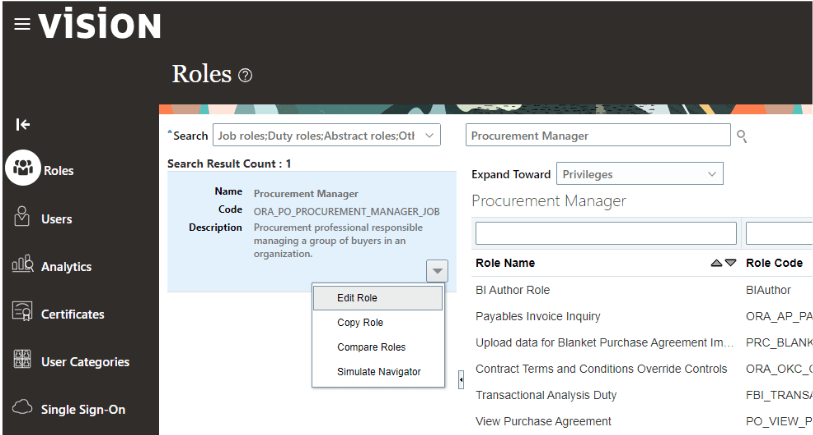
- From the Security Console, search for the Role you want to copy, for example “Procurement Manager”.
- From the dropdown next to the Role found by your search, select the option to ‘Copy Role’.
- Using the console, you can remove and add any privileges or other roles as needed.
Closing
Today’s tips and tricks only cover a small part of what Oracle Cloud offers in terms of security. But it’s a good start on your way to constructing an effective and well controlled environment where all users can perform their day to day job without having any unnecessary access.
By understanding of the fundamentals of Oracle Cloud security, you can streamline your processes and ensure you are getting the most out of your Fusion Cloud ERP.
Connect with us on our social networks: @more4apps


